In the increasingly interconnected world, cyberattacks have become a constant threat, lurking in the digital shadows and capable of crippling businesses, disrupting critical infrastructure, and even influencing geopolitical events. To visualize and understand the complex landscape of these digital conflicts, cyber attack maps have emerged as vital tools. These maps provide a dynamic, real-time representation of malicious cyber activity, offering insights into attack origins, targets, and methodologies. While often simplified for public consumption, these maps offer a glimpse into the ongoing battle for digital supremacy and the vulnerabilities inherent in our hyper-connected society.
What is a Cyber Attack Map?
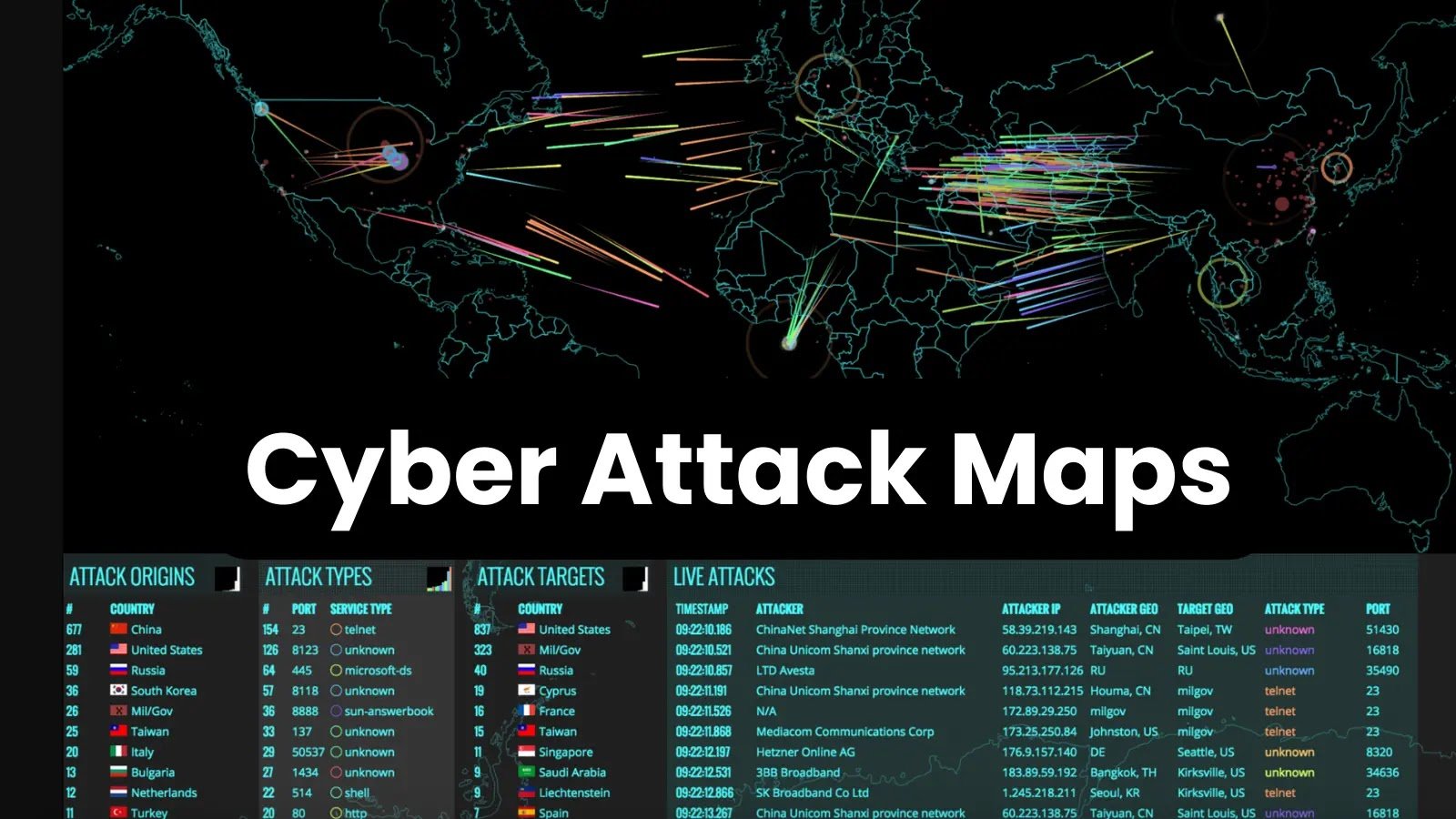
A cyber attack map is a graphical interface that visually represents ongoing cyberattacks around the world. These maps typically display:
- Source of the Attack: The geographical location from which the attack is originating. This is often represented by a country or region.
- Target of the Attack: The geographical location being targeted by the attack. This can represent a country, region, or even specific organizations.
- Type of Attack: The category of cyberattack being employed, such as DDoS attacks, malware infections, phishing attempts, or ransomware attacks.
- Attack Volume and Intensity: The scale and impact of the attack, often depicted through visual cues like line thickness, color intensity, or numerical values.
- Real-Time or Near Real-Time Data: The data presented is typically updated frequently, providing a snapshot of the current cyber threat landscape.
While the specific information and visual representation can vary depending on the provider, the core purpose remains the same: to provide a clear and concise overview of global cyber activity.
How Cyber Attack Maps Work: The Technology Behind the Visualization
The creation of cyber attack maps is a complex process that relies on a combination of data collection, analysis, and visualization techniques. Here’s a breakdown of the key components:
-
Data Collection: The foundation of any cyber attack map is the data it displays. This data is gathered from a variety of sources, including:
- Honeypots: Decoy systems designed to attract and trap attackers. These systems log information about the attacker’s techniques and targets.
- Network Traffic Analysis: Monitoring network traffic for suspicious patterns, such as unusual communication ports, large data transfers, or known malicious IP addresses.
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): Security systems designed to detect and prevent malicious activity on a network.
- Firewall Logs: Records of network traffic that has been blocked or allowed by firewalls.
- Vulnerability Scanners: Tools that identify weaknesses in systems and applications that can be exploited by attackers.
- Threat Intelligence Feeds: Subscriptions to services that provide information about known threats, including malware signatures, malicious IP addresses, and phishing websites.
- User Reports: Information reported by users who have experienced a cyberattack, such as phishing emails or malware infections.
- Publicly Available Data: Information from security blogs, news articles, and research reports.
-
Data Analysis: The raw data collected is then analyzed to identify and classify cyberattacks. This involves:
- IP Address Geolocation: Determining the geographical location of IP addresses involved in the attack. This is often done using IP geolocation databases.
- Malware Analysis: Examining malware samples to understand their functionality and identify their targets.
- Attack Pattern Recognition: Identifying common attack patterns and techniques, such as DDoS attacks, SQL injection attacks, or cross-site scripting attacks.
- Anomaly Detection: Identifying unusual or suspicious activity that may indicate a cyberattack.
-
Visualization: Finally, the analyzed data is visualized on a map using various techniques, such as:
- Geographical Representation: Displaying attack origins and targets on a world map.
- Color Coding: Using different colors to represent different types of attacks or attack severity.
- Line Thickness and Movement: Visualizing the flow of data between attack origins and targets, with line thickness indicating the volume of traffic.
- Pop-up Information: Providing detailed information about specific attacks when users click on a location on the map.
- Interactive Controls: Allowing users to filter data by attack type, target region, or time period.
The Value and Limitations of Cyber Attack Maps
Cyber attack maps offer several benefits:
- Increased Awareness: They provide a clear and accessible overview of the global cyber threat landscape, raising awareness among businesses, individuals, and governments.
- Trend Identification: By visualizing attack patterns over time, these maps can help identify emerging trends and predict future threats.
- Resource Allocation: They can help organizations prioritize security resources and focus on areas that are most vulnerable to attack.
- Public Education: Cyber attack maps can be used to educate the public about the dangers of cybercrime and the importance of cybersecurity.
However, it’s important to acknowledge the limitations of these maps:
- Simplified Representation: They often provide a simplified view of complex cyberattacks, potentially overstating or misrepresenting the actual threat.
- Data Accuracy: The accuracy of the data depends on the quality and completeness of the data sources. Inaccurate or incomplete data can lead to misleading visualizations.
- Attribution Challenges: Accurately attributing attacks to specific individuals or groups is often difficult, and the maps may not always reflect the true perpetrators.
- Limited Context: They typically provide limited context about the motives and consequences of cyberattacks.
- Potential for Misinterpretation: The visual nature of the maps can be easily misinterpreted, leading to unnecessary panic or complacency.
Examples of Prominent Cyber Attack Maps
Several organizations offer publicly accessible cyber attack maps, each with its own strengths and weaknesses. Some notable examples include:
- Kaspersky Cyberthreat Real-Time Map: This map provides a real-time view of cyberthreats detected by Kaspersky products around the world.
- Norse Corp Attack Map (Now defunct): This popular map provided a visually striking representation of cyberattacks, although it has been discontinued.
- FireEye Cyber Threat Map: FireEye’s map offers insights into attack origins, targets, and malware families.
- Akamai Real-Time Web Monitor: This map focuses on web traffic and DDoS attacks, providing insights into network performance and security.
- Fortinet Threat Map: This map visualizes global threat activity based on data collected from Fortinet’s security products.
The Future of Cyber Attack Mapping
As cyberattacks become more sophisticated and prevalent, cyber attack maps will continue to evolve. Future developments may include:
- Enhanced Data Integration: Integrating data from a wider range of sources, including social media, dark web forums, and government agencies.
- Artificial Intelligence (AI) and Machine Learning (ML): Using AI and ML to analyze data, identify patterns, and predict future attacks.
- Improved Visualization Techniques: Developing more sophisticated visualization techniques to represent complex cyberattacks in a clear and understandable way.
- Personalized Threat Intelligence: Providing users with personalized threat intelligence based on their specific industry, location, and risk profile.
- Integration with Security Tools: Integrating cyber attack maps with security tools, such as SIEM systems and firewalls, to automate threat detection and response.
Conclusion
Cyber attack maps provide a valuable window into the complex and ever-changing world of cyber threats. While it’s crucial to acknowledge their limitations, these maps offer a powerful way to raise awareness, identify trends, and prioritize security resources. As technology continues to advance, cyber attack maps will play an increasingly important role in protecting individuals, businesses, and governments from the growing threat of cybercrime. Understanding how these maps work, their strengths, and their limitations is essential for anyone seeking to navigate the increasingly perilous digital landscape. By staying informed and leveraging the insights provided by these visual representations of digital conflict, we can collectively work towards a more secure and resilient cyberspace.